Setting up VPN via SSHD
from this link
- enable
- PermitTunnel yes
- disable
- AllowTcpForwarding yes
Important: Both sides need to run as root to create the tunnel device. Thus, 'ssh -w 0:0 root@www.hentschel.net' must run as root on the client side too.
+---------------+ OpenSSH 4.3 +---------------+
| hentschel | tun0 -- Tunnel Interface -- tun0 | zm.home |
| Has a tunnel | <------------------------------->| Has a tunnel |
| and ethernet | 10.0.0.100 10.0.0.200 | and ethernet |
+-------+-------+ point to point connection +-------+-------+
eth0 | creates a bridge | eth0
198.57.187.185 | that plugs machine B | 192.168.1.100
Routable | into network A |
address | |
here | |
+-------+-------+ +-------+-------+
| Network A | | Network B |
| The Internet | | 192.168.1.1/24|
| Has internet | | Has internet |
| | | NAT gateway |
+---------------+ +---------------+
To add route from hentschel to Network B, ip route add 192.168.1.0/24 via 10.0.0.200on 'hentschel'. On zm.home, ensure IP forwarding is enabled via
sysctl net.ipv4.ip_forward, and set it to enabled in /etc/sysctl.config if not.
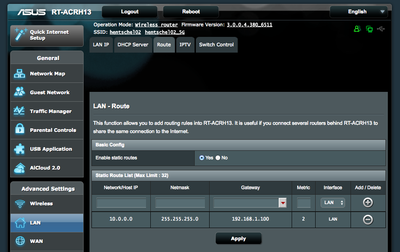
The gateway on network B needs to be modified to redirect traffic destined for host hentschel via eth0 on host zm.home. We don't redirect all internet traffic via the tunnel, just what is destined for zm.home. On the Asus router, that looks like this:
At this point, a request for any host on network B that originates on host hentschel will be answered. At the same time, traffic for hentschel from network B will be directed there via zm.home. Note that the web server on hentschel does not answer since it's interface is only set to the public interface.