(→VPN via OpenVPN) |
|||
| (10 intermediate revisions by the same user not shown) | |||
| Line 1: | Line 1: | ||
| + | == Version == | ||
| + | Current version is CentOS 6.10 - check with: <pre>cat /etc/redhat-release</pre> | ||
| + | == Changing HM password for SSH == | ||
| + | * ssh login is always 'root' | ||
| + | * server: any server under the domain | ||
| + | === Reset root/WHM password === | ||
| + | # Login to your HostMonster Control Panel | ||
| + | # Click the Performance quicklink | ||
| + | # Scroll down to the Access Management section. | ||
| + | # Click the Root tab. | ||
| + | # Under Password field, Enter the New Root Password. Click on Update. | ||
| + | |||
== Setting up VPN via SSHD == | == Setting up VPN via SSHD == | ||
from [https://help.ubuntu.com/community/SSH_VPN this link] | from [https://help.ubuntu.com/community/SSH_VPN this link] | ||
| + | One the ssh server side, modify the config: | ||
* enable | * enable | ||
** PermitTunnel yes | ** PermitTunnel yes | ||
| Line 31: | Line 44: | ||
Second, the gateway (default router) on network B needs to be modified to redirect traffic destined for host hentschel via eth0 on host zm.home. We don't redirect all internet traffic via the tunnel, just what is destined for the hentschel host. On the Asus router, that looks like this: | Second, the gateway (default router) on network B needs to be modified to redirect traffic destined for host hentschel via eth0 on host zm.home. We don't redirect all internet traffic via the tunnel, just what is destined for the hentschel host. On the Asus router, that looks like this: | ||
[[File:asus-static-route.png|600px|thumb|left|Under ''LAN''->''Route'']]<br clear=both> | [[File:asus-static-route.png|600px|thumb|left|Under ''LAN''->''Route'']]<br clear=both> | ||
| + | * the above seems flakey, sometimes the back route is incomplete. Ensuring that this works requires a route entry for each server on the home network (ugh), in the form of: | ||
| + | <pre>route add -net 10.0.0.0/24 gw 192.168.1.100</pre> | ||
To actually create the tunnel, here is what needs to happen: | To actually create the tunnel, here is what needs to happen: | ||
| Line 99: | Line 114: | ||
Also, there seem to be timing dependencies between the commands and when they execute | Also, there seem to be timing dependencies between the commands and when they execute | ||
| + | |||
| + | == Setting up VPN via OpenVPN == | ||
| + | * following this [https://www.digitalocean.com/community/tutorials/how-to-setup-and-configure-an-openvpn-server-on-centos-6 link], enumerating how far I got | ||
| + | |||
| + | # | ||
== Setting up add'l hosts via Apache ProxyPass == | == Setting up add'l hosts via Apache ProxyPass == | ||
| Line 174: | Line 194: | ||
/scripts/rebuildhttpdconf</pre> | /scripts/rebuildhttpdconf</pre> | ||
| − | * restart apache via the whm, (server.hentschel.net/whm), should be ready to go | + | * restart apache via the whm, (server.hentschel.net/whm, same login as ssh). WHM has a extra section for restarts almost all the way down. After that, should be ready to go |
== Password protection for hosts == | == Password protection for hosts == | ||
| + | * snagged from [http://www.visionfactory.com.au/blog/apache_mod_proxy_and_basic_http_authenti this link] | ||
| + | * change the vhosts file to the following | ||
| + | <pre> | ||
| + | ServerName pvr.hentschel.net | ||
| + | <Location / > | ||
| + | AuthType Basic | ||
| + | AuthUserFile "/home/hentsche/.htpasswd" | ||
| + | AuthName Limited! | ||
| + | Require valid-user | ||
| + | </Location> | ||
| + | |||
| + | ProxyRequests Off | ||
| + | <Proxy *> | ||
| + | Order deny,allow | ||
| + | Allow from all | ||
| + | </Proxy> | ||
| + | ProxyPass / http://192.168.1.101/ | ||
| + | ProxyPassReverse / http://192.168.1.101/ | ||
| + | </pre> | ||
| + | |||
| + | * create the .htpasswd file with <pre>htpasswd -c .htaccess username</pre>, add any other names w/o the '-c'. This file can be created on another host, since the server doesn't have htpasswd installed. | ||
Latest revision as of 21:37, 23 April 2019
Contents
Version
Current version is CentOS 6.10 - check with:cat /etc/redhat-release
Changing HM password for SSH
- ssh login is always 'root'
- server: any server under the domain
Reset root/WHM password
- Login to your HostMonster Control Panel
- Click the Performance quicklink
- Scroll down to the Access Management section.
- Click the Root tab.
- Under Password field, Enter the New Root Password. Click on Update.
Setting up VPN via SSHD
from this link
One the ssh server side, modify the config:
- enable
- PermitTunnel yes
- disable
- AllowTcpForwarding yes
Important: Both sides need to run as root to create the tunnel device. Thus, 'ssh -w 0:0 root@www.hentschel.net' must run as root on the client side too.
+---------------+ OpenSSH 4.3 +---------------+
| hentschel | tun0 -- Tunnel Interface -- tun0 | zm.home |
| Has a tunnel | <------------------------------->| Has a tunnel |
| and ethernet | 10.0.0.100 10.0.0.200 | and ethernet |
+-------+-------+ point to point connection +-------+-------+
eth0 | creates a bridge | eth0
198.57.xxx.xxx | that plugs machine B | 192.168.1.100
Routable | into network A |
address | |
here | |
+-------+-------+ +-------+-------+
| Network A | | Network B |
| The Internet | | 192.168.1.1/24|
| Has internet | | Has internet |
| | | NAT gateway |
+---------------+ +---------------+
First, on zm.home, ensure IP forwarding is enabled via sysctl net.ipv4.ip_forward, and set it to enabled in /etc/sysctl.config if not.
Second, the gateway (default router) on network B needs to be modified to redirect traffic destined for host hentschel via eth0 on host zm.home. We don't redirect all internet traffic via the tunnel, just what is destined for the hentschel host. On the Asus router, that looks like this:
- the above seems flakey, sometimes the back route is incomplete. Ensuring that this works requires a route entry for each server on the home network (ugh), in the form of:
route add -net 10.0.0.0/24 gw 192.168.1.100
To actually create the tunnel, here is what needs to happen:
- on zm.home
- start ssh with -w0:0 (creates tun0 interfaces on both ends), both sides need to be logged in as root
- set tun0 to up
- assign ip address to tun 0
ssh -NTCf -w0:0 root@198.57.xxx.xxx ip link set tun0 up ip addr add 10.0.0.200/24 peer 10.0.0.100 dev tun0 # not needed --> arp -Ds 10.0.0.200 eth0 pub
- once logged in on hentschel, the following needs to happen on that end
- set tun0 to up
- assign ip address to tun 0
- add route to network B
ip link set tun0 up ip addr add 10.0.0.100/24 peer 10.0.0.200 dev tun0 ip route add 192.168.1.0/24 via 10.0.0.100
At this point, a request for any host on network B that originates on host hentschel will be answered. At the same time, traffic for hentschel from network B will be directed there via zm.home. Note that the web server on hentschel does not answer since it's interface is only set to the public interface.
Automating the login
remote script on hentschel
#!/bin/bash /sbin/ip link set tun0 up /sbin/ip addr add 10.0.0.100/24 peer 10.0.0.200 dev tun0 sleep 4 /sbin/ip route add 192.168.1.0/24 via 10.0.0.100
local script on zm.home:
#!/bin/bash ssh -n -w 0:0 root@server.hentschel.net /bin/bash /root/bin/ssh-vpn-remote.sh & sleep 1 /sbin/ip link set tun0 up /sbin/ip addr add 10.0.0.200/24 peer 10.0.0.100 dev tun0
Here a few tricks at this link
Add the following to ~/.ssh/config (client side):
host targetserver
ControlMaster auto
ControlPath ~/.ssh/cm_sockets/%r@%h:%p
Then this will work:
$ ssh -fNT -Llocalport:remoteserver:remoteport targetserver $ ssh -O check targetserver Master running (pid=23450) $ <do your stuff> $ ssh -O exit targetserver Exit request sent. $ ssh -O check targetserver Control socket connect(/home/sorin/.ssh/cm_socket/sorin@192.0.2.3:22): No such file or directory
Also, there seem to be timing dependencies between the commands and when they execute
Setting up VPN via OpenVPN
- following this link, enumerating how far I got
Setting up add'l hosts via Apache ProxyPass
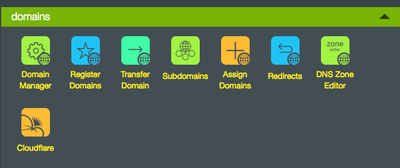
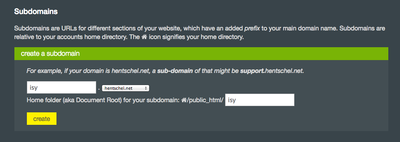
server.hentschel.net is running CentOS. Files are in non-standard locations. Hints are from this link To setup isy.hentschel.net on port 443:
- create a 'subdomain' on the hoster.
- this stuff is done via cPanel, so need to find the location where cPanel expects the config files. The httpd.conf file under /usr/local/apache.conf gives some hints:
# To customize this VirtualHost use an include file at the following location
# Include "/usr/local/apache/conf/userdata/std/2/hentsche/isy.hentschel.net/*.conf"
Create the directory that this path entry is looking for, and chown to the web user:
root@server.hentschel.net [hentsche]# mkdir isy.hentschel.net root@server.hentschel.net [hentsche]# chown hentsche:hentsche isy.hentschel.net
Add a file there that looks like:
ServerName isy.hentschel.net
ProxyRequests On
# Order deny,allow
# Allow from all
ProxyPass / http://192.168.1.99/
ProxyPassReverse / http://192.168.1.99/
# Order allow,deny
# Allow from all
and name it isy.hentschel.net.conf. Make sure to chown to hentsche this file too.
- Important: If there should be SSL access, add the same file to /usr/local/apache/conf/userdata/ssl/2/hentsche/isy.hentschel.net/. Then you only need to do the steps below once.
- run the verifier /scripts/verify_vhost_includes --show-test-output:
root@server.hentschel.net [isy.hentschel.net]# /scripts/verify_vhost_includes --show-test-output Testing /usr/local/apache/conf/userdata/std/2/hentsche/zm.hentschel.net/zm.hentschel.net.conf...ok [TEST RESULTS] [Mon Mar 27 06:08:21 2017] [warn] NameVirtualHost 198.57.187.185:443 has no VirtualHosts [Mon Mar 27 06:08:21 2017] [warn] NameVirtualHost 198.57.187.185:80 has no VirtualHosts Syntax OK [/TEST RESULTS] Testing /usr/local/apache/conf/userdata/std/2/hentsche/isy.hentschel.net/isy.hentschel.net.conf...ok [TEST RESULTS] [Mon Mar 27 06:08:21 2017] [warn] NameVirtualHost 198.57.187.185:443 has no VirtualHosts [Mon Mar 27 06:08:21 2017] [warn] NameVirtualHost 198.57.187.185:80 has no VirtualHosts Syntax OK [/TEST RESULTS]
- commit the changes via /scripts/verify_vhost_includes --commit /scripts/ensure_vhost_includes --all-users
root@server.hentschel.net [isy.hentschel.net]# /scripts/verify_vhost_includes --commit /scripts/ensure_vhost_includes --all-users Argument 1 did not match (?^:^--(.)) at /usr/local/cpanel/3rdparty/perl/524/lib64/perl5/cpanel_lib/Class/Std.pm line 438. Testing /usr/local/apache/conf/userdata/std/2/hentsche/zm.hentschel.net/zm.hentschel.net.conf...ok Testing /usr/local/apache/conf/userdata/std/2/hentsche/isy.hentschel.net/isy.hentschel.net.conf...ok
- next is the cpanel distiller /usr/local/cpanel/bin/apache_conf_distiller --update
root@server.hentschel.net [isy.hentschel.net]# /usr/local/cpanel/bin/apache_conf_distiller --update warn [apache_conf_distiller] Unable to determine domain 198.57.187.185 ownership. Attempting lookup on domain 57.187.185 (manually added domain). warn [apache_conf_distiller] Unable to determine domain 198.57.187.185 ownership. Setting user to 'nobody'. warn [apache_conf_distiller] Unable to determine domain _wildcard_.hentschel.net ownership. Attempting lookup on domain hentschel.net (manually added domain). Distilled successfully
- and finally a script that rebuilds the apache config via /scripts/rebuildhttpdconf
root@server.hentschel.net [isy.hentschel.net]# /scripts/rebuildhttpdconf Built /usr/local/apache/conf/httpd.conf OK
- everything together w/o the screen output
/scripts/verify_vhost_includes --show-test-output /scripts/verify_vhost_includes --commit /scripts/ensure_vhost_includes --all-users /usr/local/cpanel/bin/apache_conf_distiller --update /scripts/rebuildhttpdconf
- restart apache via the whm, (server.hentschel.net/whm, same login as ssh). WHM has a extra section for restarts almost all the way down. After that, should be ready to go
Password protection for hosts
- snagged from this link
- change the vhosts file to the following
ServerName pvr.hentschel.net
<Location / >
AuthType Basic
AuthUserFile "/home/hentsche/.htpasswd"
AuthName Limited!
Require valid-user
</Location>
ProxyRequests Off
<Proxy *>
Order deny,allow
Allow from all
</Proxy>
ProxyPass / http://192.168.1.101/
ProxyPassReverse / http://192.168.1.101/
- create the .htpasswd file with
htpasswd -c .htaccess username
, add any other names w/o the '-c'. This file can be created on another host, since the server doesn't have htpasswd installed.